MAG normally runs through Stalker Portal, but if for whatever reason it is necessary to run IPTV on a MAG device through M3U, then this tutorial is for you.
The use of Internet Protocol technology and a two-way set-top box means that security messages-including authentication messages, confirmations, and decryption codes-can travel easily in both directions, to and from an IPTV set-top box, to multiple destinations in the operator’s network. Download Link: https://www.upload.ee/files/9566806/IPTVBruteforce1.1byAzimut500.exe.html.
Basically, running curious tests aside, there are two reasons why this tutorial and running IPTV through M3U on a MAG is vital:
1-If you are an IPTV provider reading this, you sure have had an experience in which the MAG MAC addresses registered on your panel gets leaked with the streaming line of each MAC extracted and posted online. This is due to a bug in Stalker_Portal and for the time being almost all IPTV CMS service have not had the solution for it. Crackers brute force the stalker portal url of your cms and crack MACs one by one. Some CMS softwares have a script function to block IPs of cracking devices and works to some extent but not enough. Therefore, most IPTV providers are discontinuing the support of all Stalker devices/apps and moving their clients to M3U Streaming lines only. If the client has no other device to run IPTV on, with this tutorial, you can help them run the service using M3U on their MAG.
2-Looking it from end-user's point of view, if the chosen IPTV provider only provides M3U streaming lines and the client only has a MAG as device, learning this method can be handy. Another reason for a client would be whether they prefer the interface of Smart IPTV app but they do not have a Smart TV or an android device and all they have got is a MAG device.
So how this basically works?
All MAG devices run based on a stalker portal. IPTV provider gives the portal url which looks like http://anyprovider.com:port/c/, and activate client's MAC address on their system and it starts loading the portal.
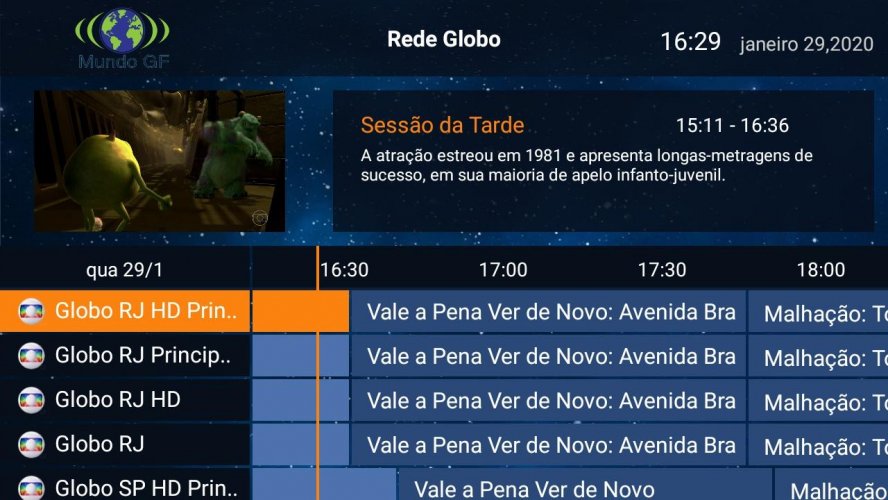
In this case, we will use Smart IPTV app own portal address instead of IPTV provider's address and this will link our MAG device to Smart IPTV system. Once it's done, upon running the portal, Smart IPTV app interface pops up, showing your MAG MAC address and asking for activation. From this point, it will be the usual procedure of activating Smart IPTV on their portal, pairing the MAC with M3U address from the IPTV provider.
Some key points before we proceed with the setup:
1-Smart IPTV says their portal only works on 'Aura HD' MAG types, basically MAG 250/254/270. But we do recommend to try this on your MAG device and see if it works. Tests show even MAG4xx can work with this.
2-There are preparation steps advised by Smart IPTV. We recommend to do this on your MAG device and see if it works by default. If not, there are two steps explained at the end of this tutorial to be done. But first do as follows and if does not work, then refer to those two steps at the end of this tutorial and retry.
The setup procedure is the same as when a stalker portal URL is added to any MAG but let's go through the steps as we always do.
1-From the Main Menu select Settings
2-Choose System Settings
3-Select Servers
4-Click Portals
5-Name the portal whatever you like and in the URL field put http://mag.siptv.app/ This is the Stalker Portal URL of Smart IPTV app.
Basically, this address links our MAG device to Smart IPTV app own Database and interface.
6-Now go back one step and Restart Portal.
7-Once the portal loads, Smart IPTV app shows up. As highlighted above, the app has detected our MAG box MAC address and paired it to the app. Now we simply need to use this MAC address to pair it with a M3U url from the IPTV provider at https://siptv.app/mylist/
So, once again:
A-App has detected a MAC address 00:1A:79:6c:ec:8f in this case. For any MAG device it sure varies.
B-We should have a M3U, preferably a M3U_Plus also known as 'M3U With Options' from the IPTV provider.
8-This step is just a regular step for pairing a M3U with Smart IPTV app. Do as above and finally click Send.
Now reload the portal on MAG and Smart IPTV app should load with the channel listing.
Below are the General Remote Control buttons function when using Smart IPTV app.
- P+/P and Arrow buttons - navigate through pages, groups and channels
- ОК, Up/Down - load channel list in Play mode; show information/channel history
- INFO, INFOx2 - show programme information
- Number Keys - direct channel selection
- '0' - previous channel in Play mode
- BACK - hide channel list and info; go back to primary list; reload portal
- EXIT - go back to main portal
- RATIO, MENU - picture ratio
- PLAY - permanent infobar
- STOP - relaunch stream
- RED - settings in primary list, change audio track, where possible
- GREEN, GUIDE - EPG + archive; play mode in video player
- YELLOW - all channels, show digital clock in Play mode
- BLUE - show groups; settings in Play mode; subtitles in video player
Above are the regular steps to install and run the app. If in some cases running the app stumbles into errors like Time Syncing issues or Display Resolution errors, two steps should be taken: A: Setting the right Video Output Mode/Graphic Resolution and B: Setting the Right NTP settings

A: Setting the right Video Output Mode and Graphic Resolution
A_1: From the settings page go to System Settings and then select Video.
A_2: Set Video Output Mode to 1080i-60 and Graphic Resolution to 1280x720.
B: Setting the Right NTP settings
B_1: From System Settings go to Servers
B_2: Select General
B_3: NTP stands for Network Time Protocol. Almost all devices on planet earth run their time zones using a NTP server. Thats why all devices with internet access have exactly the same timing.
There are many NTP servers all around the world. For instance if you are in the UK, your preferred NTP server should be uk.pool.ntp.org.
Visit the NTP Pool Project own webpage and pick your desired NTP server: https://www.pool.ntp.org/zone/europe
That should be it. Is it not? ask questions below.
The brute force attack is still one of the most popular password-cracking methods. Nevertheless, it is not just for password cracking. Brute force attacks can also be used to discover hidden pages and content in a web application. This attack is basically “a hit and try” until you succeed. This attack sometimes takes longer, but its success rate is higher.
In this article, I will try to explain brute force attacks and popular tools used in different scenarios for performing brute force attacks to get desired results.
What is a brute force attack?
A brute force attack when an attacker uses a set of predefined values to attack a target and analyze the response until he succeeds. Success depends on the set of predefined values. If it is larger, it will take more time, but there is a better probability of success.
The most common and easiest to understand example of the brute force attack is the dictionary attack to crack passwords. In this, the attacker uses a password dictionary that contains millions of words that can be used as a password. The attacker tries these passwords one by one for authentication. If this dictionary contains the correct password, the attacker will succeed.
In a traditional brute force attack, the attacker just tries the combination of letters and numbers to generate a password sequentially. However, this traditional technique will take longer when the password is long enough. These attacks can take several minutes to several hours or several years, depending on the system used and length of password.
To prevent password cracking from brute force attacks, one should always use long and complex passwords. This makes it hard for attackers to guess the password, and brute force attacks will take too much time. Account lockout is another way to prevent the attacker from performing brute force attacks on web applications. However, for offline software, things are not as easy to secure.
Similarly, for discovering hidden pages, the attacker tries to guess the name of the page, sends requests and sees the response. If the page does not exist, it will show a 404 response; on a success, the response will be 200. In this way, it can find hidden pages on any website.
Brute force is also used to crack the hash and guess a password from a given hash. In this, the hash is generated from random passwords and then this hash is matched with a target hash until the attacker finds the correct one. Therefore, the higher the type of encryption (64-bit, 128-bit or 256-bit encryption) used to encrypt the password, the longer it can take to break.

Reverse brute force attack

A reverse brute force attack is another term that is associated with password cracking. It takes a reverse approach in password cracking. In this, the attacker tries one password against multiple usernames. Imagine if you know a password but do not have any idea of the usernames. In this case, you can try the same password and guess the different usernames until you find the working combination.
Now, you know that a brute-forcing attack is mainly used for password cracking. You can use it in any software, any website or any protocol which does not block requests after a few invalid trials. In this post, I am going to add a few brute force password-cracking tools for different protocols.
Popular tools for brute force attacks
Aircrack-ng
I am sure you already know about the Aircrack-ng tool. This is a popular brute force wifi password cracking tool available for free. I also mentioned this tool in our older post on most popular password-cracking tools. This tool comes with WEP/WPA/WPA2-PSK cracker and analysis tools to perform attacks on Wi-Fi 802.11. Aircrack-ng can be used for any NIC which supports raw monitoring mode.
It basically performs dictionary attacks against a wireless network to guess the password. As you already know, the success of the attack depends on the dictionary of passwords. The better and more effective the password dictionary is, the more likely it is that it will crack the password.
It is available for Windows and Linux platforms. It has also been ported to run on iOS and Android platforms. You can try it on given platforms to see how this tool can be used for brute force wifi password cracking.
Download Aircrack-ng here.
John the Ripper
John the Ripper is another awesome tool that does not need any introduction. It has been a favorite choice for performing brute force attacks for a long time. This free password-cracking software was initially developed for Unix systems. Later, developers released it for various other platforms. Now, it supports fifteen different platforms including Unix, Windows, DOS, BeOS and OpenVMS.
You can use this either to identify weak passwords or to crack passwords for breaking authentication.
This tool is very popular and combines various password-cracking features. It can automatically detect the type of hashing used in a password. Therefore, you can also run it against encrypted password storage.
Basically, it can perform brute force attacks with all possible passwords by combining text and numbers. However, you can also use it with a dictionary of passwords to perform dictionary attacks.
Download John the Ripper here.
Rainbow Crack
Rainbow Crack is also a popular brute-forcing tool used for password cracking. It generates rainbow tables for using while performing the attack. In this way, it is different from other conventional brute-forcing tools. Rainbow tables are pre-computed. It helps in reducing the time in performing the attack.
The good thing is that there are various organizations which have already published the pre-computer rainbow tables for all internet users. To save time, you can download those rainbow tables and use them in your attacks.
This tool is still in active development. It is available for both Windows and Linux and supports all latest versions of these platforms.
Download Rainbow Crack and read more about this tool here.
L0phtCrack
L0phtCrack is known for its ability to crack Windows passwords. It uses dictionary attacks, brute force attacks, hybrid attacks and rainbow tables. The most notable features of L0phtcrack are scheduling, hash extraction from 64-bit Windows versions, multiprocessor algorithms and network monitoring and decoding. If you want to crack the password of a Windows system, you can try this tool.
Download L0phtCrack here.
Ophcrack
Ophcrack is another brute-forcing tool specially used for cracking Windows passwords. It cracks Windows passwords by using LM hashes through rainbow tables. It is a free and open-source tool.
In most cases, it can crack a Windows password in a few minutes. By default, Ophcrack comes with rainbow tables to crack passwords of less than 14 characters which contain only alphanumeric characters. Other rainbow tables are also available to download.
Ophcrack is also available as LiveCD.
Download Ophcrack here.
Hashcat
Hashcat claims to be the fastest CPU-based password cracking tool. It is free and comes for Linux, Windows and Mac OS platforms. Hashcat supports various hashing algorithms including LM Hashes, MD4, MD5, SHA-family, Unix Crypt formats, MySQL and Cisco PIX. It supports various attacks including brute force attacks, combinator attacks, dictionary attacks, fingerprint attacks, hybrid attacks, mask attacks, permutation attack, rule-based attacks, table-lookup attacks and toggle-case attacks.
Download Hashcat here.
DaveGrohl
DaveGrohl is a popular brute-forcing tool for Mac OS X. It supports all available versions of Mac OS X. This tool supports both dictionary attacks and incremental attacks. It also has a distributed mode that lets you perform attacks from multiple computers to attack on the same password hash.
This tool is now open-source and you can download the source code.
Download DaveGrohl here.
Ncrack
Ncrack is also a popular password-cracking tool for cracking network authentications. It supports various protocols including RDP, SSH, HTTP(S), SMB, POP3(S), VNC, FTP and Telnet. It can perform different attacks including brute-forcing attacks. It supports various platforms including Linux, BSD, Windows and Mac OS X.
Download Ncrack here.
THC Hydra
THC Hydra is known for its ability to crack passwords of network authentications by performing brute force attacks. It performs dictionary attacks against more than 30 protocols including Telnet, FTP, HTTP, HTTPS, SMB and more. It is available for various platforms including Linux, Windows/Cygwin, Solaris 11, FreeBSD 8.1, OpenBSD, OSX and QNX/Blackberry.
Download THC Hydra here.
Conclusion
These are a few popular brute-forcing tools for password cracking. There are various other tools are also available which perform brute force on different kinds of authentication. If I just give an example of a few small tools, you will see most of the PDF-cracking and ZIP-cracking tools use the same brute force methods to perform attacks and crack passwords. There are many such tools available for free or paid.
Brute-forcing is the best password-cracking method. The success of the attack depends on various factors. However, factors that affect most are password length and combination of characters, letters and special characters. This is why when we talk about strong passwords, we usually suggest that users have long passwords with a combination of lower-case letters, capital letters, numbers and special characters. It does not make brute-forcing impossible but it does make it difficult. Therefore, it will take a longer time to reach to the password by brute-forcing.
Awesome Modules Of Recon-ng Used For Web Recon Testing ...
Almost all hash-cracking algorithms use the brute force to hit and try. This attack is best when you have offline access to data. In that case, it makes it easy to crack and takes less time.
Iptv Brute-force How To Use Screen
Brute force password cracking is also very important in computer security. It is used to check the weak passwords used in the system, network or application.
IPTV Brute-Force - Search And Brute Force Illegal IPTV Server ...
The best way to prevent brute force attacks is to limit invalid logins. In this way, attacks can only hit and try passwords only for limited times. This is why web-based services start showing captchas if you hit the wrong passwords three times or they will block your IP address.